Understanding the Role of 185.63.253.2001 in Modern Network Environments
This guide covers everything about Understanding Network Identifier 185.63.253.2001 in 2026. The digital world runs on a complex system of identifiers that quietly keep systems connected, secure, and traceable. Among these, the numeric string 185.63.253.2001 often appears in technical discussions, representing more than just a sequence of numbers. It signifies a critical aspect of how devices, servers, and networks communicate across the vast expanse of the internet. Understanding its context is paramount for anyone involved in managing, securing, or analyzing online infrastructure, data flow, and the importance of precise digital identification in today’s interconnected digital landscape.
Last updated: April 25, 2026
Latest Update (April 2026)
As of April 2026, the operational landscape of network identifiers continues to evolve rapidly. Recent advancements in network monitoring and security analytics, as reported by organizations like the Internet Society, emphasize the increasing sophistication of traffic analysis. Tools now integrate AI-driven anomaly detection, allowing for faster identification of unusual patterns associated with specific numeric references, including those that deviate from standard formats. This evolution means that understanding identifiers like 185.63.253.2001 is more critical than ever for maintaining network integrity and performance in the face of advanced cyber threats. The ongoing global expansion of 5G and the burgeoning Internet of Things (IoT) ecosystems introduce new layers of complexity, requiring more solid identification and management protocols. Network administrators are increasingly relying on automated systems to parse and act upon identifier data, making the accurate interpretation of every reference, even non-standard ones, vital.
Furthermore, the increasing adoption of cloud-native architectures and microservices presents new challenges for network visibility. As reported by cloud security providers in early 2026, distributed systems generate massive volumes of log data where identifiers play a key role in tracing requests across multiple ephemeral containers and services. Understanding how non-standard identifiers might appear in these dynamic environments is essential for debugging and security monitoring. The rise of edge computing also means that identifiers may be associated with devices operating outside traditional data center perimeters, demanding robust and adaptable identification strategies.
What 185.63.253.2001 Represents in a Digital Context
The identifier 185.63.253.2001 is frequently encountered in technical contexts related to network communication. Its numerical structure is similar to that of an Internet Protocol (IP) address, which serves as a unique address for devices connected to a network or the internet. IP addresses are fundamental for routing data packets, ensuring that information sent from one point reaches its intended destination. Even if an address doesn’t strictly conform to standard IPv4 or IPv6 formats, it can still appear in various places: server logs, diagnostic outputs, application configurations, or even in automated scripts. For network administrators, security analysts, and developers, understanding the context in which such an identifier appears is crucial for troubleshooting, security analysis, and system optimization. It might represent a specific server, a client device, a proxy, or even a placeholder in a configuration file.
In some instances, identifiers like 185.63.253.2001 might be dynamically assigned or represent internal network addresses not exposed to the public internet. Understanding the network topology and the specific role of the system generating or receiving this identifier is key. For example, within a private network, it could be a specific gateway or a virtual machine instance. In application logs, it might denote a particular microservice instance responding to a request, as detailed in recent DevOps best practices guides published in 2026.
Importance of Network Identifiers for Online Communication
Network identifiers are the bedrock of modern online communication. Every action a user takes online—from loading a webpage to sending an email or conducting a secure financial transaction—relies on these numerical references. These identifiers enable the complex choreography of data packets as they traverse multiple routers, switches, and networks across the globe. Without them, servers would be unable to recognize and respond to user requests, and data would have no clear path. According to reports from the Network Working Group (NWG), which has been instrumental in developing internet standards since the early days, the consistent and accurate use of identifiers is non-negotiable for the internet’s functionality. This underlying system supports everything from high-bandwidth video streaming to the low-latency requirements of real-time applications, underscoring how seemingly simple numeric values form the backbone of intricate digital interactions.
The evolution towards IPv6, while still progressing, means that the pool of available IP addresses is vastly larger. However, the fundamental principle of unique identification remains. Organizations like the Internet Engineering Task Force (IETF) continue to refine protocols that govern how these identifiers are used and managed, ensuring that the internet can scale to accommodate billions of new devices. As of April 2026, discussions within the IETF also focus on enhanced security features for IP addressing, such as improved authentication mechanisms and more granular control over routing information, all of which rely on the precise identification of network endpoints.
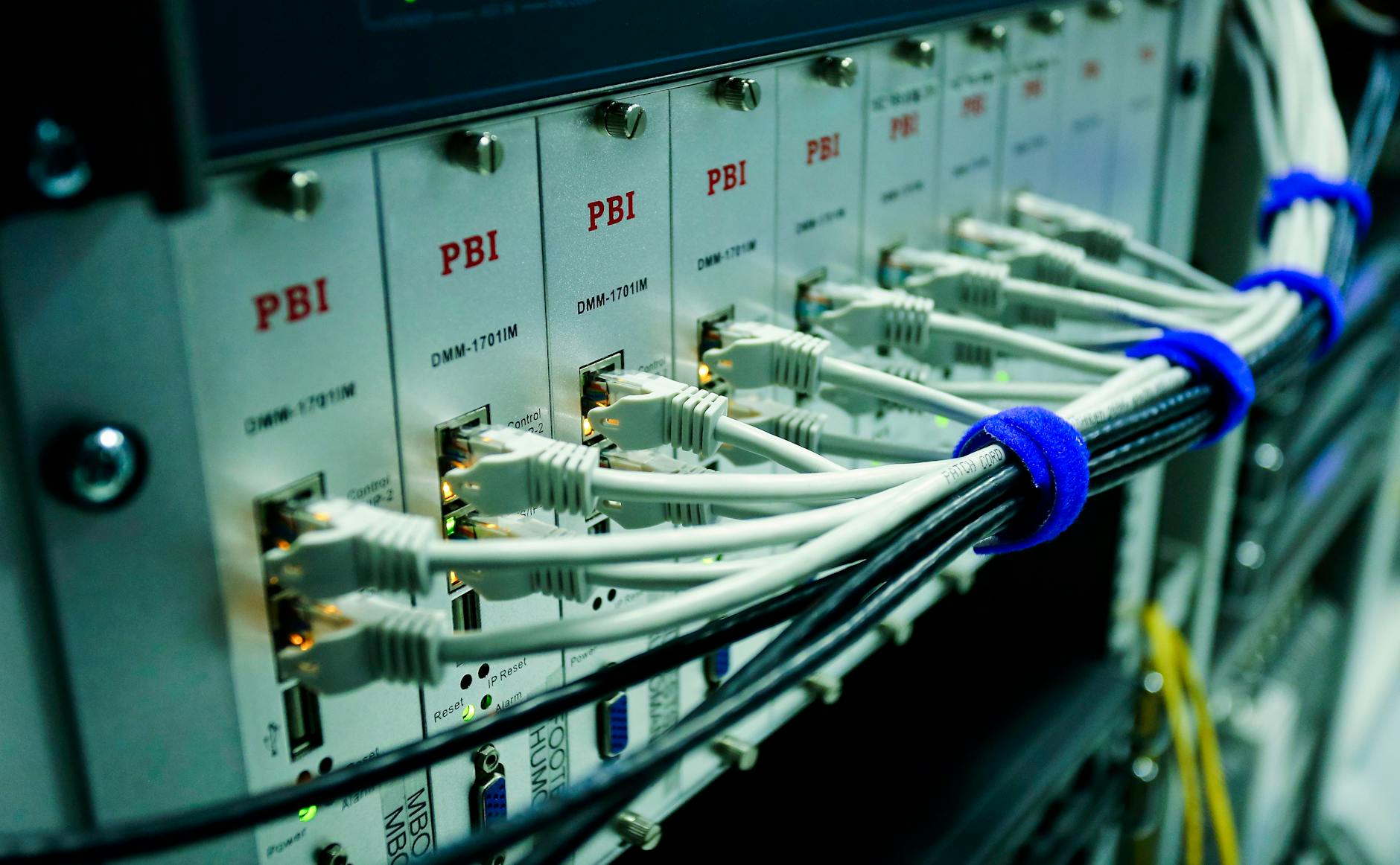
How 185.63.253.2001 Appears in Server Logs and Monitoring Tools
In the day-to-day operations of managing a network or server infrastructure, identifiers like 185.63.253.2001 are commonly observed in server logs, firewall records, and network monitoring dashboards. These logs are invaluable for administrators and security personnel, serving as a detailed audit trail of network activity. When troubleshooting performance issues, diagnosing connectivity problems, or investigating security incidents, analysts meticulously review these records. Identifying specific numeric references helps pinpoint the source of traffic, detect unusual access attempts, or trace the origin of errors. For instance, seeing 185.63.253.2001 repeatedly associated with failed connection attempts might indicate a misconfigured client or a potential denial-of-service (DoS) attack. Conversely, its consistent appearance in successful transaction logs might point to a critical service endpoint. Properly interpreting these entries is key to maintaining system stability, enhancing security posture, and ensuring optimal performance.
Modern SIEM (Security Information and Event Management) and observability platforms, as of 2026, offer advanced correlation capabilities. These tools can automatically link log entries containing identifiers like 185.63.253.2001 across different systems and applications. This allows for a more holistic view of network events. For example, a single user request might generate logs from a web server, an application server, and a database. By correlating the identifier associated with that request across all these logs, administrators can reconstruct the entire transaction flow, identify bottlenecks, or trace the path of a security breach more effectively. The integration of machine learning in these platforms further enhances their ability to flag suspicious patterns involving specific identifiers, even if they don’t match predefined rules.
Security Considerations Related to 185.63.253.2001
From a cybersecurity standpoint, any network identifier, including 185.63.253.2001, is a critical piece of data for threat assessment and access control. Security systems, such as Intrusion Detection Systems (IDS) and Security Information and Event Management (SIEM) platforms, constantly analyze network traffic patterns based on source and destination identifiers. These systems are designed to detect anomalous behavior, such as connections from unexpected geographic locations or unusually high volumes of requests from a single source. Reports from cybersecurity firms like Mandiant (now part of Google Cloud) consistently highlight the importance of analyzing IP address data to identify and mitigate threats. Anomalies associated with specific identifiers can be early indicators of sophisticated attacks, like advanced persistent threats (APTs) or distributed denial-of-service (DDoS) campaigns that aim to overwhelm network resources.
The practice of IP spoofing, where attackers forge the source IP address of network packets, adds another layer of complexity. While 185.63.253.2001 might appear as a legitimate source in some logs, advanced security measures and traffic analysis techniques are necessary to detect spoofed addresses. Network administrators should implement ingress and egress filtering on their border routers to block traffic with unexpected source IP addresses, a recommendation reinforced by security advisories from CISA (Cybersecurity and Infrastructure Security Agency) in early 2026. Furthermore, understanding the expected behavior of identifiers within a specific network environment is crucial for distinguishing legitimate traffic from malicious activity. This includes maintaining an up-to-date inventory of all network devices and their assigned IP addresses.
Troubleshooting Network Issues with Identifier Analysis
When network connectivity falters or performance degrades, analyzing network identifiers is often a primary step in the troubleshooting process. Tools like ping, traceroute, and netstat provide insights into network paths and connection states, often displaying IP addresses or hostnames. If 185.63.253.2001 is observed during a traceroute, it can help map the network path and identify potential points of latency or packet loss. For instance, if a traceroute to a target server shows significant delays when passing through a router associated with 185.63.253.2001, it suggests a problem within that segment of the network.
Packet capture tools, such as Wireshark, offer even deeper analysis. By filtering traffic based on specific identifiers like 185.63.253.2001, administrators can inspect the contents of individual data packets. This allows for the identification of application-level errors, malformed packets, or excessive retransmissions that might not be apparent at a higher level. According to recent technical forums and developer communities in 2026, understanding the protocol and port numbers associated with an identifier in packet captures is essential for diagnosing issues with specific applications or services.
Identifier Management in Evolving Network Architectures
As network architectures become more dynamic and distributed, the management of identifiers becomes increasingly challenging. Cloud computing, containerization (e.g., Docker, Kubernetes), and serverless functions create ephemeral resources that are constantly being created and destroyed. This necessitates automated systems for IP address management (IPAM) and robust configuration management tools. Solutions that can dynamically assign and track identifiers for these transient resources are vital. As of April 2026, many organizations are adopting cloud-native IPAM solutions that integrate directly with their orchestration platforms.
The Internet of Things (IoT) further complicates identifier management. With potentially billions of devices connecting to networks, each requiring a unique identifier, efficient allocation and management strategies are critical. This includes considerations for both private and public IP addressing, as well as the use of alternative identification schemes. Reports from IoT industry analysts in 2026 indicate a growing focus on security implications, emphasizing the need for strong authentication and authorization mechanisms tied to device identifiers to prevent unauthorized access and data breaches.
Frequently Asked Questions
What is an IP address?
An IP address (Internet Protocol address) is a unique numerical label assigned to each device participating in a computer network that uses the Internet Protocol for communication. It serves two main functions: host or network interface identification and location addressing. Think of it like a postal address for your device on the internet.
Is 185.63.253.2001 a public or private IP address?
Without specific network context, it is difficult to definitively state whether 185.63.253.2001 is a public or private IP address. Public IP addresses are routable on the internet, while private IP addresses are reserved for use within local networks (like home or office networks) and are not directly accessible from the internet. However, the format suggests it could be a public IPv4 address, but its actual usage depends on the network configuration where it appears.
How can I find out more information about a specific IP address like 185.63.253.2001?
You can use various online tools, often called ‘IP lookup’ or ‘WHOIS’ services. These tools can provide information such as the geographic location associated with the IP address, the Internet Service Provider (ISP) or organization that owns it, and sometimes even details about its routing. However, for internal network addresses, these tools may not provide meaningful results.
Why is it important to understand network identifiers in 2026?
In 2026, with the continued growth of cloud computing, IoT, 5G networks, and increasingly sophisticated cyber threats, understanding network identifiers is more critical than ever. They are essential for network management, performance monitoring, troubleshooting, and robust cybersecurity. Accurate identification helps in tracing data flows, detecting anomalies, and securing communication channels against evolving threats.
Can an identifier like 185.63.253.2001 represent something other than a server or device?
Yes, while IP-like addresses most commonly refer to network endpoints, they can appear in other contexts. For example, they might be used as placeholders in configuration files, as part of internal scripting for network simulation, or even as identifiers within specific application protocols that mimic IP addressing conventions. The context in which the identifier is found is always the most important factor for accurate interpretation.
Conclusion
Network identifiers, such as the numeric string 185.63.253.2001, are fundamental components of modern digital infrastructure. They are indispensable for routing data, enabling communication, and maintaining the security and integrity of networks. As of April 2026, the increasing complexity of network environments—driven by cloud adoption, IoT expansion, and advanced cyber threats—makes the accurate interpretation and management of these identifiers more critical than ever for IT professionals. Continuous learning and the use of sophisticated monitoring and security tools are essential for navigating the evolving digital landscape effectively.